Session & Identity Assurance
Workforce Data Is Only as Trustworthy as Its Identity Layer
ZoikoTime continuously verifies identity, session integrity, device, and location — transforming workforce activity into defensible, audit-grade truth.
The Hidden Failure
The Hidden Failure in Workforce Systems
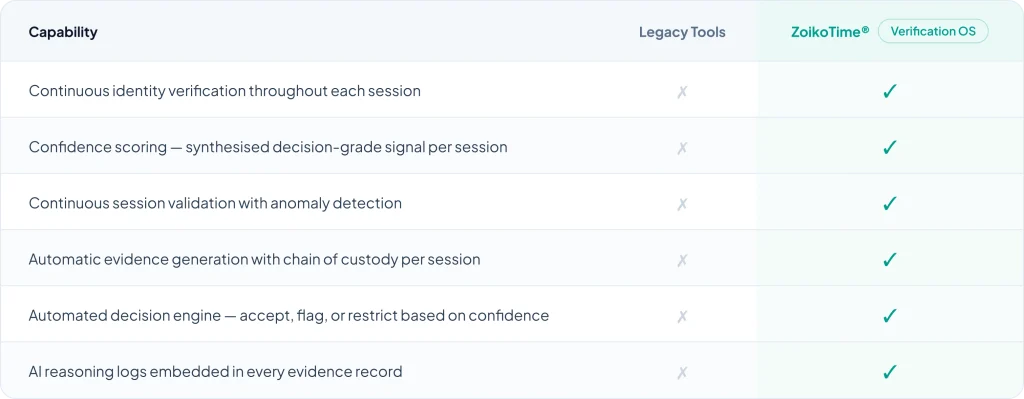
Most systems assume identity. ZoikoTime verifies it — continuously, across every session, every device, and every location.
Most systems are built on assumed identity. ZoikoTime is built on verified truth.
System Guarantees
What ZoikoTime Guarantees
Four defensible, audit-facing commitments built into the system architecture — not policy statements.

No session is accepted without identity validation
Every session requires a verified identity signal before it is treated as valid — no exceptions, no defaults to assumed presence.

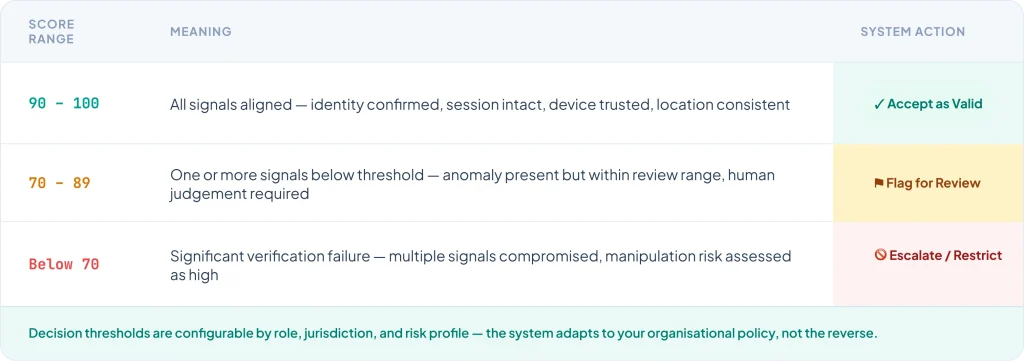
Every session is assigned a confidence score
A synthesised 0–100 confidence score is calculated for every session in real time — providing a single, actionable measure of session trustworthiness.

Low-confidence activity is automatically flagged
Sessions falling below policy-defined thresholds are flagged for review or escalated automatically — without requiring human initiation.

All sessions produce traceable evidence
Every session — valid, flagged, or rejected — generates a tamper-evident evidence record with full context, confidence score, and AI reasoning attached.
The Verification Engine
Four Layers. One Confidence Score.
Each verification layer captures a distinct signal. All signals are synthesised by the Confidence Engine into a single decision- grade score — the core of workforce truth.

Identity Layer
Ensures the right individual is present — via authentication signals, biometric indicators, and behavioural patterns.

Session Layer
Monitors session continuity, activity patterns, and temporal consistency throughout the working period.

Device Layer
Validates device fingerprint, trust status, and consistency across sessions — detecting substitution or compromise.

Location Layer
Verifies geographical consistency against expected patterns, policy requirements, and prior session history.
Decision Engine
From Signals to Decisions
ZoikoTime does not just observe — it decides. Every confidence score maps to an automated decision outcome that protects payroll, compliance, and audit integrity.
Failure Scenarios
What Happens When Something Is Not Right
Regulator-grade realism — how ZoikoTime responds to the manipulation patterns and edge cases that standard systems miss entirely.

VPN Masking Detected
- Location signal inconsistency detected — claimed location does not match network origin
- VPN routing pattern identified — location cannot be verified against policy
- Confidence score drops below threshold — session flagged for review

Device Switching Mid-Session
- Device fingerprint change detected mid-session — new device not matching registered profile
- Device trust status revoked — mismatch triggers risk signal elevation
- Session continuity broken — escalation workflow initiated automatically

Idle Session with Activity
- Activity signals detected during an idle- flagged session — behaviour inconsistent with genuine user presence
- AI engine identifies pattern as anomalous — classification: potential automation or proxy
- Session flagged, confidence score reassessed, review workflow triggered
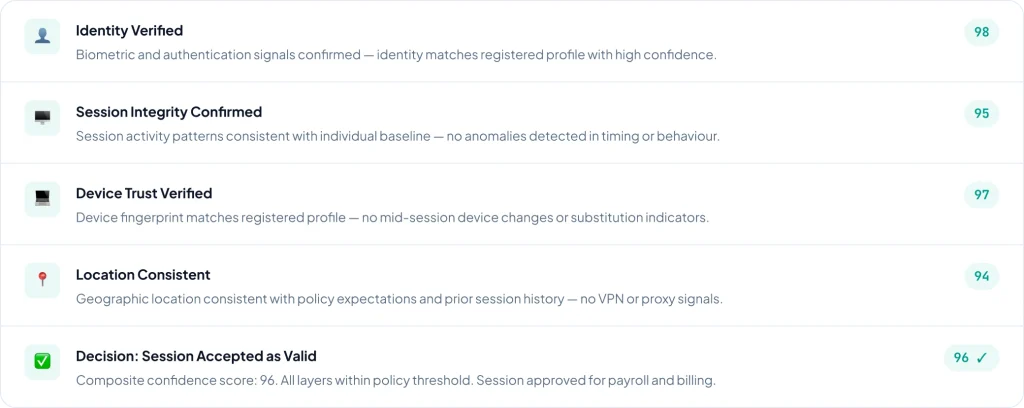
Live Walkthrough
See the System Think in Real Time
Toggle between a valid and flagged session to see exactly how ZoikoTime processes signals, assigns confidence, and reaches a decision.
Evidence Engine
Verification Becomes Defensible Evidence
Every session — valid, flagged, or rejected — automatically generates a structured evidence record that directly supports payroll, audit, and legal processes.

Payroll Defensibility
Only verified sessions at policy confidence thresholds qualify — payroll is backed by evidence, not assumption.

Audit Support
Every evidence record includes identity validation, session integrity, confidence score, and AI reasoning — audit-ready by design.

Legal Dispute Resolution
Tamper-evident records with chain of custody provide court- admissible evidence for any employment or billing dispute.

Why ZoikoTime
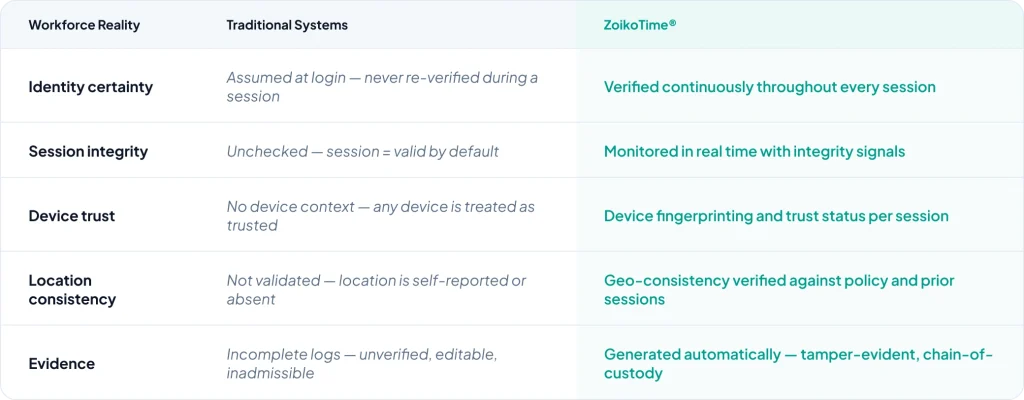
Why Traditional Systems Fail
Legacy tools were not designed to verify identity — they were designed to record time. The gap between the two is where financial and compliance risk lives.
Verification Without Surveillance
We Verify Signals — Not Invade Privacy
Identity assurance and privacy protection are not in conflict in ZoikoTime — both are foundational design requirements, not competing priorities.

Configurable Sensitivity
Verification intensity is configurable by role, risk profile, and jurisdiction — applying only the level of assurance required for each context, not a one- size-fits-all surveillance model.

Full User Transparency
Every individual can understand what signals are collected, why they are collected, and how they influence their session confidence — visible through the ZoikoTime Transparency Center.

Signal-Based, Not Surveillance-Based
ZoikoTime captures the minimum signals required to verify a session — not screenshots, keystrokes, or continuous screen monitoring. Assurance without invasion is the design principle.
Enterprise Impact
What This Means for Your Organisation
CFO
Eliminates Unverified Payroll Spend
Every payroll period is backed by verified session evidence — unverified sessions never qualify for payment, eliminating the primary source of payroll leakage across distributed workforces.
CIO
Ensures Data Integrity
Workforce data integrity is established at the source — every data point linked to a verified identity and session, providing a trusted foundation for every downstream analysis and report.
Compliance
Enables Audit Defensibility
Every session generates a tamper- evident evidence record with AI reasoning — providing the structured, verifiable documentation that regulators, auditors, and legal proceedings require.
Get Started
If Identity Is Uncertain, Everything Else Is at Risk
ZoikoTime gives your organisation the continuous verification infrastructure needed to make every second of recorded work defensible — for payroll, for audit, and for legal proceedings.