Data Processing Framework Built for Compliance, Transparency, and Global Operations
ZoikoTime provides a structured data processing model aligned with
GDPR, CCPA, and global data protection frameworks — designed for enterprise contracting and regulatory clarity.
ZoikoTime acts strictly as a data processor, executing customer-defined policies within a governed and compliant framework.
How Data Processing Works in ZoikoTime
All processing is governed by customer-defined policies and enforced through system-level controls — not discretionary decisions made by ZoikoTime.

Policy Definition
You define processing scope, rules, and purposes

Data Input
Workforce data collected under your lawful basis

Processing
ZoikoTime executes your defined policies only

Controls & Logging
System-enforced controls and immutable audit logs

Output & Review
Reports and evidence available to you as Controller
ZoikoTime does not determine the purposes or means of processing — those are defined and controlled exclusively by the customer.
What Is Processed and Why
Processing scope is defined and configurable by customer policy. ZoikoTime applies data minimisation at the architecture level — only what is necessary for defined purposes is processed.
Data Categories Processed
Identity Data
Worker identity for session attribution — name, role, unique identifier, employment status. No biometric data collected or processed.
Activity & Session Data
Session start/end times, activity signals, continuity indicators, and confidence scoring data generated during verified workforce sessions.
Device & System Data
Device identifiers, operating system signals, network indicators, and system metadata used for session verification and fraud detection.
Contextual Signals
Optional
Location and environment signals — collected only when explicitly enabled by customer policy and with appropriate worker transparency.
Purpose of Processing
Workforce Assurance
Session verification, confidence scoring, anomaly detection, and payroll integrity assurance — the core governance function of the platform.
Performance Intelligence
Aggregated workforce performance signals used to generate management intelligence — processed at population level, not for individual surveillance.
Audit Documentation
Generation of tamper-evident evidence records supporting workforce audit, legal proceedings, regulatory inspection, and payroll dispute resolution.
Compliance Reporting
Production of compliance documentation for regulatory, governance, and contractual purposes — formatted for immediate regulatory and legal use.
Security Infrastructure Article 32 Compliant
ZoikoTime's security measures are implemented at the architecture level — independently verified against SOC 2 Type II, ISO 27001, and GDPR Article 32 requirements.

Encryption
AES-256 encryption at rest applied from point of data capture. TLS 1.3 enforced in transit across all system pathways. Encryption is architectural — cannot be disabled by configuration.

Role-Based Access Control
Least-privilege access enforced at platform architecture. Every access event validated against role assignment. Admin access requires MFA re-authentication. All access events logged immutably.

Immutable Audit Logging
All processing actions, data access events, and configuration changes logged to an append-only, tamper-evident audit store. SHA-256 integrity verification on every record read.

Continuous Anomaly Monitoring
Real-time anomaly detection across all processing operations — session signals, access patterns, and system events monitored continuously against defined baselines. Human escalation for all defined threshold breaches.

Business Continuity
Redundant processing infrastructure with defined RTO and RPO commitments. Regular resilience testing and documented incident response procedures — maintained under ISO 22301 business continuity principles.

Regular Testing & Review
Annual penetration testing by independent third parties. Quarterly internal vulnerability assessment. Continuous security monitoring with defined escalation thresholds and remediation timelines.
Sub-Processor Transparency and Governance
All sub-processors are contractually bound to equivalent data protection obligations — with advance notification of any changes and a defined right to object before new sub-processors are engaged.
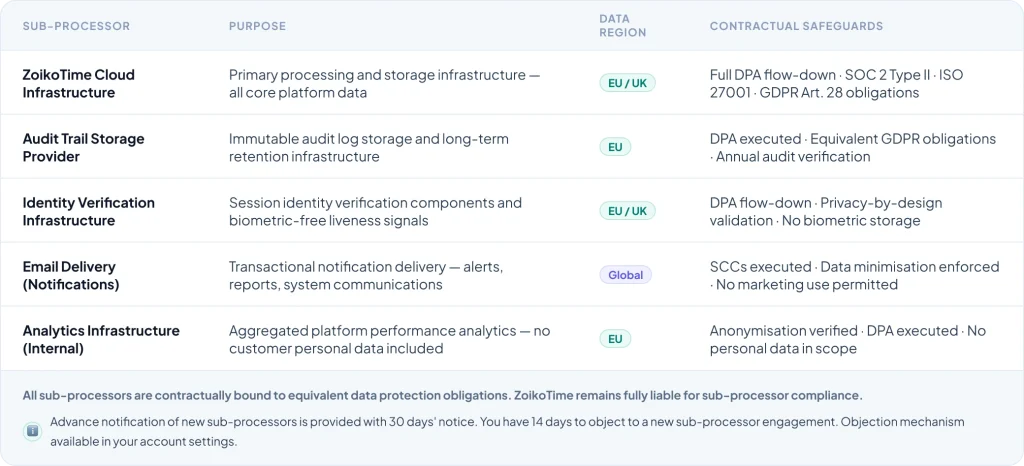
Cross-Border Data Transfer Safeguards
Where data is transferred outside the EEA or UK, ZoikoTime applies appropriate safeguards — with pre-executed SCCs available for immediate counter-signature and jurisdiction-specific addenda included.

Standard Contractual Clauses
EU Commission SCCs (2021 version) and UK IDTA executed for all relevant third-country transfers. Module 2 (Controller to Processor) and Module 3 (Processor to Processor) both available. Pre-signed and ready for counter- signature.

Adequacy Decisions
Where applicable, data transfers are structured to rely on EU Commission or UK adequacy decisions — providing the simplest and most legally robust basis for cross-border transfers for the relevant destination countries.

Supplementary Measures
For transfers to high-risk jurisdictions, supplementary measures are implemented in accordance with EDPB Recommendations 01/2020 — including technical measures (encryption), contractual measures, and organisational controls.
Enabling You to Fulfil Rights Requests Efficiently
ZoikoTime provides the tools to respond to all GDPR Chapter III data subject rights requests — with structured workflows, automated data extraction, and documented response audit trails.
Article 15
Right of Access
Structured data access export — all personal data processed for a specific data subject, formatted for immediate provision to the data subject in a readable format.
Article 16
Right to Rectification
Correction workflow for inaccurate personal data — controlled update process with audit trail confirming the rectification and the original data state prior to amendment.
Article 17
Right to Erasure
Targeted deletion capability — specific data subject records erasable on instruction, with deletion confirmation record and exemption management for data subject to legal hold obligations.
Article 18
Right to Restriction
Restriction flag applied to specified records — data retained but processing halted pending the resolution of a contest or objection, with restriction event logged to the audit trail.
Article 20
Right to Portability
Structured data export in machine-readable format (JSON, CSV) — covering all data provided by or about the data subject, formatted for transmission to an alternative controller.
Article 21
Right to Object
Objection workflow with assessment documentation — controller-side review process with outcome documentation, and restriction of processing pending review where required.
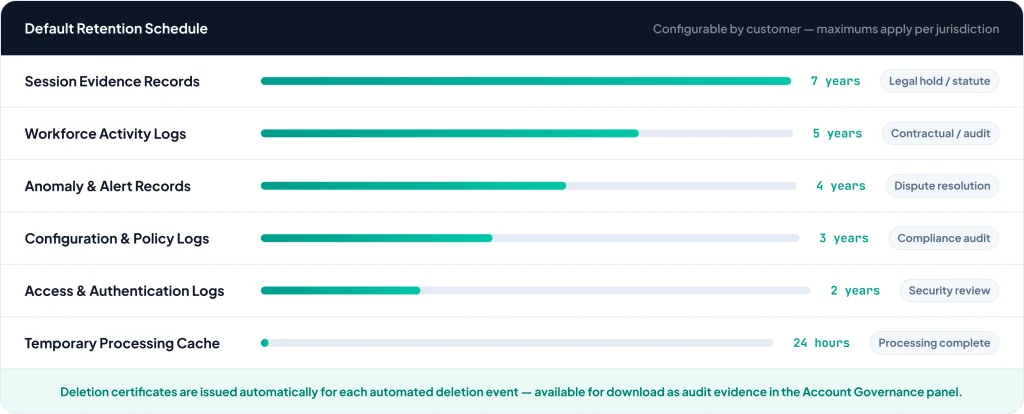
Configurable Retention Automated Deletion
Retention periods are configurable by customer policy within the bounds of applicable legal requirements. Automated deletion is enforced at the end of each retention period — with deletion certificates issued for each deletion event.
Download the Complete Compliance Pack
Everything your legal, procurement, and compliance teams need to evaluate and contract ZoikoTime's data processing — in a single structured download.
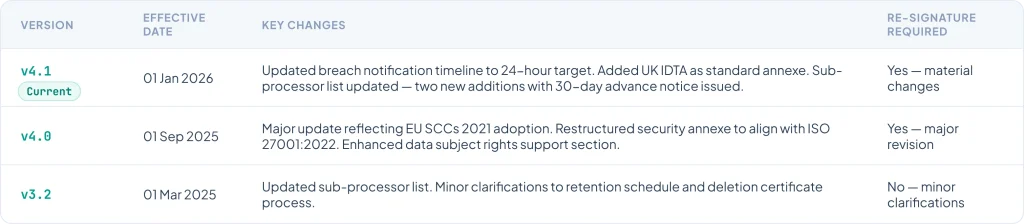
DPA Version Control
Direct Access to ZoikoTime's Privacy Team

Legal Inquiry
Contract review, DPA questions, liability scope, or legal interpretation — routed directly to ZoikoTime's legal counsel with a 24-hour response SLA.

Compliance Discussion
GDPR alignment questions, regulatory obligation mapping, audit support, or compliance framework queries — answered by ZoikoTime's compliance specialists.

DPA Negotiation
Enterprise clients requiring bespoke DPA terms — direct engagement with the legal team for structured redlining and clause negotiation. Initial response within 2 business days.
Deploy ZoikoTime With Full Data Processing Confidence
The DPA documentation suite is designed to accelerate legal review — not extend it. Everything your legal and compliance teams need is available for immediate download and review.