Evidence Capture
A System of Record for
Workforce Truth
ZoikoTime captures, constructs, and preserves forensic-grade evidence for every workforce action — ensuring every decision can be verified, audited, and legally defended.
The Problem
Why Workforce Data Fails Under Legal and Audit Scrutiny
Most organisations have data — but data is not evidence. When challenged, the absence of proof-grade records becomes an existential risk.

No System of Record
Multiple conflicting datasets across HR systems, time tools, and productivity platforms create inconsistency that cannot withstand legal challenge — no single source of verifiable truth exists.

Weak Integrity
Logs that can be edited, overwritten, or accessed without audit trails have zero evidentiary value. Without tamper-evidence and integrity verification, data is not proof — it is opinion.

No Legal Admissibility
Without traceable origin, context preservation, and chain of custody, workforce records cannot be used in legal proceedings, regulatory inspections, or formal dispute resolution processes.
Data without proof is not evidence. And without evidence, decisions cannot be defended— in court, in audit, or in any formal challenge.
The Infrastructure
The Evidence Infrastructure Layer
Six integrated layers that transform raw workforce activity into structured, tamper-evident, court-ready evidence — automatically, at the moment of every event.
1
Event Capture Layer
Comprehensive Activity Recording
- Captures every workforce action — sessions, decisions, anomalies, and transitions
- Records the precise timing, device context, and environmental signals of each event
- Policy-triggered capture ensures only relevant and purposeful events are recorded
Nothing is missed. Every event enters the evidence pipeline from the moment it occurs.
2
Context Enrichment Layer
Comprehensive Activity Recording
- Attaches verified identity, jurisdiction, and policy context to every event record
- Location, timestamp, and work environment are linked at the point of capture
- Policy framework in effect at the time of the event is permanently associated
Context is not reconstructed later — it is captured at the moment of truth.
3
Evidence Construction Engine
Evidence Creation — Not Logging
- Transforms raw event data into structured evidence objects with full supporting context
- Each object is self-contained — origin, identity, context, and policy all embedded
- Evidence is constructed to meet forensic investigation standards from the point of creation
This is evidence creation — not data storage. The fundamental distinction.
4
Integrity & Hashing Layer
Tamper-Evident Records
- Captures every workforce action — sessions, decisions, anomalies, and transitions
- Any modification — however minor — is instantly detectable on integrity verification
- Hash verification is performed on every retrieval, ensuring records remain pristine
Immutable by design. Any tampering is immediately and permanently detectable.
5
Chain of Custody Engine
Complete Record Lifecycle Tracking
- Tracks every access, transfer, and interaction with each evidence record from creation
- Every custody event is timestamped, attributed to a verified identity, and immutable
- Chain of custody export available in formats accepted by legal and regulatory bodies
Every hand this record has passed through is documented — permanently.
6
Retrieval & Presentation Layer
Audit-Ready Evidence Output
- Structured evidence views formatted for legal review, regulatory inspection, and HR proceedings
- Export packages include evidence object, chain of custody, and integrity verification in one bundle
- Role-based access controls determine what each viewer can see and export
Evidence delivered in the structure required — not raw data that must be interpreted.
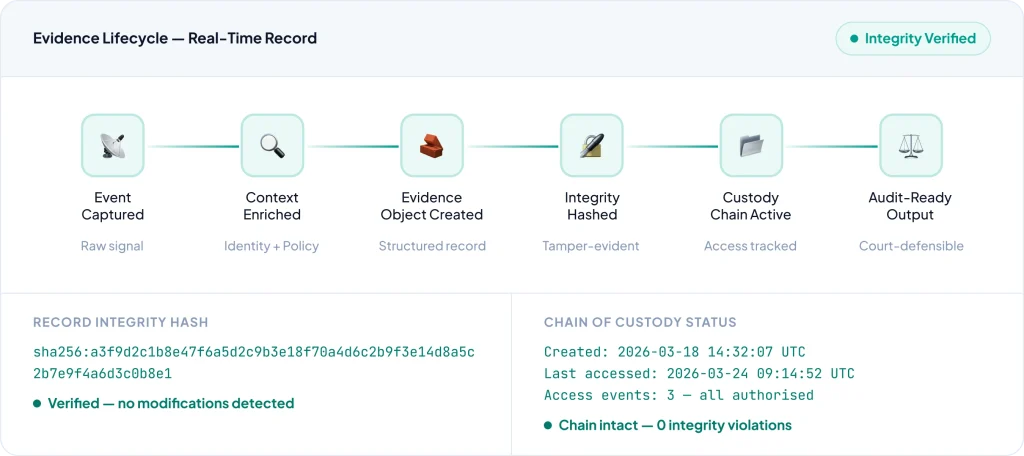
Chain of Custody
A Complete, Verifiable Record Lifecycle
Every evidence record has a complete lifecycle — from the moment of creation through every access, transfer, and retrieval — meeting forensic investigation standards at every step.

Legal Admissibility
Evidence That Stands Up in Legal Proceedings
ZoikoTime is designed with legal admissibility as a foundational requirement — not a feature added after the fact. Every evidence record meets the standards required for formal legal proceedings.

Traceable Origin
Every record has a cryptographically verifiable origin — when it was created, by which system, and under what policy context.

Integrity Verification
Hash-based tamper detection ensures any modification — however minor — is permanently and instantly detectable on review.

Complete Context Preservation
Identity, jurisdiction, policy framework, and environmental context are embedded in every record — nothing is reconstructed after the fact.

Legal Review & Proceedings
Evidence packages structured to meet court and tribunal requirements — origin verifiable, integrity confirmed, chain of custody complete, and policy context fully documented for legal counsel.

Dispute Resolution
Verified evidence that resolves employment disputes, contractor disagreements, and performance challenges — providing a defensible, impartial record that reduces litigation risk and resolution time.

Regulatory Inspection
Export-ready evidence packages formatted for regulatory submission — labour authority inspections, data protection audits, financial compliance reviews — delivered in the structure regulators require.
Selective Disclosure
Share What Is Needed — Protect What Is Sensitive
Evidence access is not binary. ZoikoTime provides granular control over who sees what — enabling organisations to share the right evidence with the right people, without exposing sensitive data unnecessarily.

Controlled Access
Every evidence record has access policies — who can view, export, or share it, and under what conditions. Access is logged to the chain of custody automatically.

Data Redaction
Sensitive fields — personal identifiers, unrelated third-party data, legally protected information — can be redacted before disclosure without affecting the integrity of the evidence record.

Role-Based Visibility
Different roles receive different views of the same evidence. Auditors see the full record. Managers see operational summaries. Legal counsel sees evidence packages. All from one system.
Real-Time Generation
Evidence Created at the Moment of Truth
Evidence is not assembled retrospectively from logs. It is constructed at the instant the event occurs — no delay, no reconstruction, no gaps.
01
Action Occurs
A workforce event — session, decision, anomaly — takes place in real time anywhere in the system.
02
Context Captured
Identity, jurisdiction, policy, device, and environment are attached to the event record at capture.
03
Evidence Constructed
The Evidence Construction Engine builds a structured evidence object — self- contained and complete.
04
Integrity Verified
A cryptographic hash is applied. The record is now tamper-evident and integrity-verifiable at any future point.
05
Stored & Ready
The sealed evidence object is stored with its custody chain active — immediately available for audit, legal review, or export.
Evidence Coverage
Comprehensive, Structured Evidence Coverage
Five distinct evidence types — each with its own structured object format, verification layer, and audit output — covering every dimension of workforce activity.

Activity Evidence
What happened — every session, task, and operational event with full execution context.

Identity Evidence
Who performed it — verified identity attribution with authentication signals and device context.

Context Evidence
Where and when — location, time, jurisdiction, and environmental context at the moment of the event.

Decision Evidence
Why it happened — the decision, the policy applied, the approver, and the documented justification.

Anomaly Evidence
What went wrong — anomaly signals, fraud indicators, and policy violations with detection context.
Audit Simulation
What an Auditor Receives
When an audit request arrives, ZoikoTime provides a fully structured, integrity-verified evidence package — not raw data that must be manually assembled and interpreted.
Audit Request
Regulatory audit — attendance records and policy compliance for worker USR-00441 covering the period 01 Jan 2026 – 31 Mar 2026. Chain of custody required.

Instant retrieval
Evidence package assembled in under 2 seconds — no manual compilation

Structured output
Formatted to regulatory submission standards — no interpretation required
Lifecycle Management
Manage Evidence From Creation to Retention
Evidence that is retained beyond its purpose creates risk. ZoikoTime provides the full lifecycle controls needed to align evidence management with GDPR, data governance, and legal hold requirements.

Retention Policies
Define retention schedules by evidence type, jurisdiction, and business purpose — ensuring records are held for exactly as long as required and no longer, in compliance with applicable regulations.

Archival
Evidence approaching end-of- retention is automatically archived to cost-efficient, compliant storage — with integrity and chain of custody maintained throughout, and retrieval available on demand.

Secure Deletion
At end of retention, records are securely and verifiably deleted — with a deletion certificate added to the chain of custody to confirm compliance and protect against future liability.
Dispute Resolution
Resolve Disputes With Verified Evidence
When disputes arise — whether from employees, contractors, regulators, or legal counsel — ZoikoTime provides the verified, structured evidence needed to resolve them quickly and defensibly.

Fast Resolution
Verified evidence eliminates ambiguity — disputes are resolved on fact, not recollection, dramatically reducing resolution time and legal cost.

Defensible Outcomes
Every decision supported by verified evidence is inherently defensible — protecting the organisation in any formal challenge or escalation.

Impartial Record
Evidence constructed at the moment of the event — before any dispute existed — is inherently impartial and cannot be accused of retrospective construction.
Enterprise Impact
What This Means for Your Organisation
Measurable outcomes for the executives accountable for financial defensibility, legal exposure, and audit readiness.
CFO
Financial Defensibility
Verified evidence for every payroll decision, billing record, and financial action — eliminating disputes, reducing legal costs, and providing a defensible audit trail for every financial outcome.
General Counsel
Legal Admissibility
Court-ready evidence with verified origin, intact chain of custody, and cryptographic integrity — ensuring your organisation can defend any workforce decision in legal proceedings with confidence.
Internal Audit
Complete Visibility
Instant access to structured evidence packages for any period, worker, or event — with integrity verification built in, reducing audit preparation time from weeks to minutes.
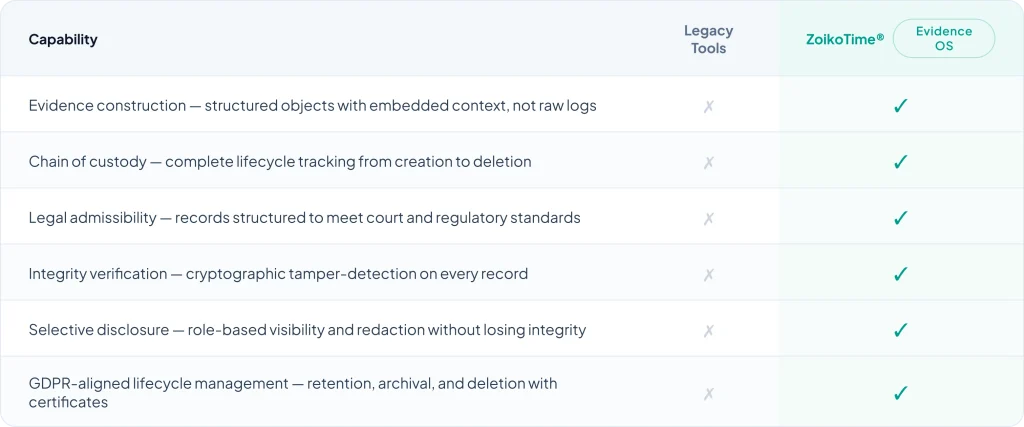
Why ZoikoTime
Why Logs Are Not Evidence
Legacy tools create logs. ZoikoTime creates evidence. The gap between the two determines whether your organisation can defend its decisions when it matters most.
Get Started
If You Cannot Prove It, You Cannot Defend It
ZoikoTime gives your organisation the forensic evidence infrastructure needed to verify, audit, and legally defend every workforce decision — with records built to the standard that legal proceedings demand.