Compliance Infrastructure for Workforce Operations
Verifiable, Continuous, and Audit-Ready
ZoikoTime enables organisations to operate with confidence through policy-driven controls, structured evidence generation, and alignment with global regulatory frameworks.
ZoikoTime transforms compliance from periodic validation into continuous, system-enforced assurance.
- SOC 2 Type II–Aligned Controls
- ISO 27001 Control Framework
- GDPR & Privacy Alignment
- Audit-Ready Evidence Generation
- Continuous Compliance Monitoring
How Compliance Works in ZoikoTime
Compliance is enforced at the point of operation — not reconstructed after the fact. Every stage generates structured, auditable evidence automatically.

Policy Definition
Rules, thresholds, jurisdiction settings

Control Enforcement
System-level, real-time enforcement

Evidence Generation
Tamper-evident, timestamped records

Monitoring & Alerts
Rules, thresholds, jurisdiction settings

Audit & Reporting
On-demand exports, regulator- ready
Compliance is enforced at the point of operation — not reconstructed after the fact. Every stage generates structured evidence automatically.
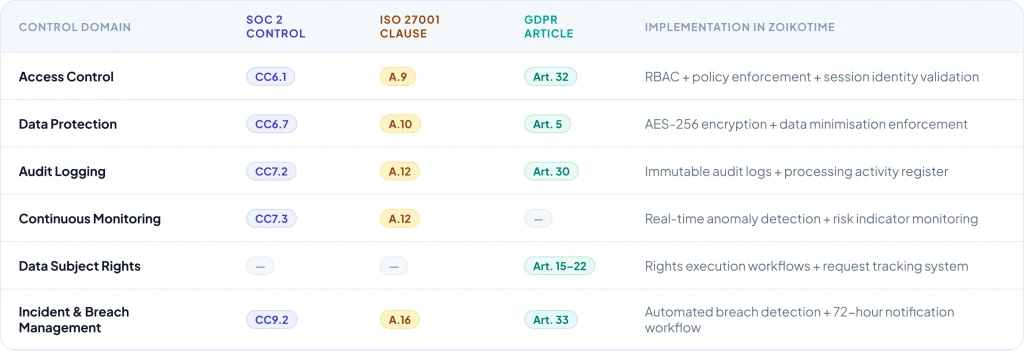
Line-by-Line Control Mapping Across Frameworks
Big 4 audit-level control documentation — click any row to expand the full control logic, system behaviour, and evidence generated for each mapped control.
How Controls Are Enforced In Practice
Controls are executed by the system in real time not dependent on manual adherence, individual discretion, or periodic review. Here is the enforcement logic for the three primary control areas.

Access Control Enforcement
Every access event is validated against the role assignment matrix before execution — not logged after. Unauthorised access is blocked, not just audited.
- Role-based permissions enforced at platform architecture — cannot be bypassed by configuration
- Least-privilege default — access must be explicitly granted, not assumed
- Session identity validated at every access event — not just at login
- All access events logged immutably with full context and actor identity
Controls are executed — not assumed to be in place.

Policy Enforcement Logic
Employer-configured governance policies are enforced at the system level — consistently applied across every session, worker, and jurisdiction without manual intervention.
- Configurable rules defined by the organisation through the Policy Engine
- Automated validation against policy at every session event — no gaps, no exceptions
- Exception handling — policy breach detected, flagged, and escalated immediately
- Policy configuration change log — every policy modification tracked and auditable
Policy enforcement is systemic — not dependent on individual discipline.

Data Handling Controls
Data processing constraints are enforced at the architecture level — ensuring data minimisation, purpose limitation, and retention compliance regardless of user or admin action.
- Encryption enforced at capture — AES- 256 at rest, TLS 1.3 in transit, always on
- Retention schedules enforced automatically per jurisdiction — deletion certificates issued
- Access logging for every data interaction — no silent data access in any pathway
- Cross-purpose use prevented systemically — not reliant on policy instruction
Data controls are architectural — they cannot be disabled or bypassed.
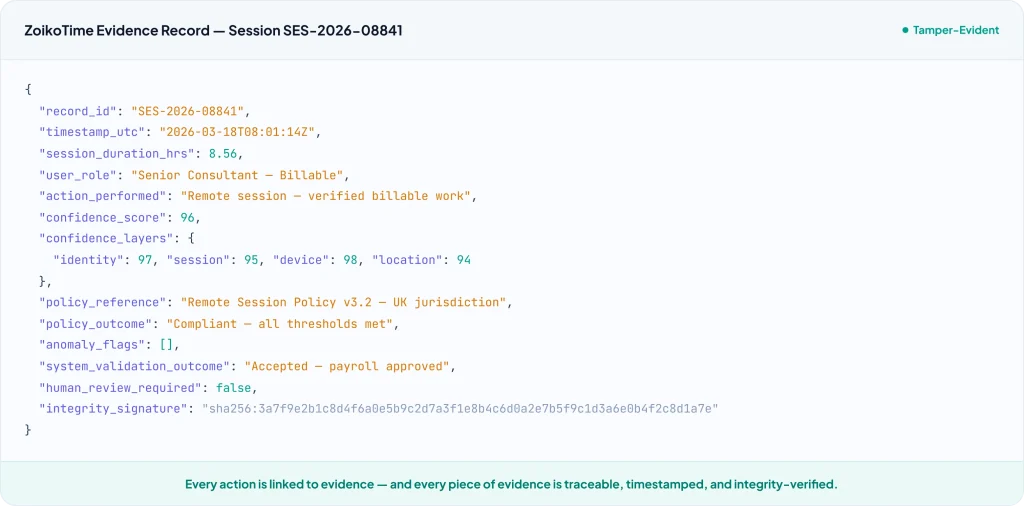
Structured Evidence Generation Every Record
Every action in ZoikoTime is linked to a structured evidence record timestamped, policy-referenced, integrity-signed, and traceable. This is the schema of a standard session evidence record.
How ZoikoTime Responds to Real Audit Scenarios
Three real-world audit scenarios — each showing exactly what an auditor requests and what ZoikoTime produces in response. This is deal-closing material for compliance teams.
Wage & Hour Audit Scenario
A regulatory authority requests proof of hours worked for a sample group of workers over a specified period — a common wage compliance audit requirement in regulated sectors. Before ZoikoTime, this took HR teams weeks to prepare. With ZoikoTime, it takes under 4 minutes.
Auditor Request
"Provide verified proof of hours worked and policy compliance for 50 workers across the period 01–31 March 2026, including any flagged or disputed sessions."
ZoikoTime generates a structured evidence package automatically — no manual preparation, no reconstruction from incomplete records, no gaps.
Real-Time Compliance Monitoring
ZoikoTime monitors compliance continuously — not periodically. Anomalies, policy breaches, and risk indicators are detected and escalated in real time, before they become compliance incidents.

Anomaly Detection
Continuous statistical and adversarial pattern analysis — detecting manipulation, fraud, and policy deviation signals in real time. Every anomaly classified, scored, and routed to human review before any consequential action is taken.

Policy Breach Alerts
Immediate alerting when a configured policy threshold is breached — working time violations, jurisdiction non- compliance, access threshold exceedance. Notifications routed to the appropriate governance function automatically.

Risk Indicator Dashboard
Real-time risk indicator monitoring across all active workforce populations — surfacing emerging risk patterns before they become incidents, and providing the governance context required for proactive remediation.
Third-Party Verified Compliance Posture
ZoikoTime's compliance posture is not a self-assessment — it is validated by independent third-party audit and certification against the relevant standards.

SOC 2 Type II
Annual independent audit against the Trust Services Criteria — security, availability, processing integrity, confidentiality, and privacy.

ISO 27001
Information security management system certified against ISO/IEC 27001:2022 — covering all applicable Annex A controls.

GDPR Aligned
Privacy-by-design architecture aligned to GDPR, UK GDPR, and CCPA/CPRA — with DPA, processing register, and DPIA documentation available.

EU AI Act
High-risk AI system compliance framework in place — human-in- command model, explainability requirements, and conformity assessment documentation available.
Compliance Documentation Immediately Available

Compliance Overview
Complete compliance architecture overview — controls, frameworks, and alignment evidence structured for procurement and legal review.

Control Mapping Document
Full control-by-control mapping across SOC 2, ISO 27001, GDPR, CCPA, and EU AI Act — with implementation and evidence for each control.

Audit Pack
Structured evidence pack for audit and regulatory inspection — session evidence examples, control effectiveness report, and chain of custody documentation.

Policy Framework Guide
Policy Engine configuration framework — governance policies, jurisdiction rule sets, and compliance configuration guide for enterprise deployment.
Compliance You Can
Defend Not Just Claim
ZoikoTime provides the control framework, evidence infrastructure, and audit documentation that regulators, auditors, and legal teams require — not a compliance statement, a verifiable system.