Integrity & Anomaly Detection
A Real-Time Integrity Control System for Workforce Data
ZoikoTime continuously verifies, detects, and controls workforce behaviour — ensuring your data remains accurate, defensible, and protected from manipulation at any scale.
The Risk
What Happens When Workforce Data Is Compromised
Manipulated workforce data is not an isolated incident — it undermines every decision, financial record, and audit outcome that depends on it.

Financial Impact
Payroll leakage, inflated costs, and fraudulent billing accumulate silently — each undetected manipulation a drain that compounds across teams, periods, and jurisdictions before it surfaces in a reconciliation or audit.

Decision Risk
Incorrect business decisions made from manipulated data — resourcing, performance management, compliance reporting — cause downstream damage that extends far beyond the original manipulation event.

Audit Failure
Data that has been manipulated — even if subtly — cannot be defended in audit, legal proceedings, or regulatory inspection. The inability to prove integrity is itself a compliance failure.
If your workforce data can be manipulated, your entire decision framework is compromised — every output built on that data inherits the risk.
The System
The Integrity Intelligence System
Six layers that detect manipulation, assess risk, and enforce control — from verified data capture through to forensic-grade evidence for every anomaly.
1
Verified Input Layer
Clean Data at the Source
- Session validation confirms every data point before it enters the integrity pipeline
- Identity assurance links all activity to a verified worker — no anonymous inputs
- Policy-aligned capture rules prevent unauthorised data from entering the system
Integrity begins at capture — not retrospectively during review.
2
Behavioural Baseline Engine
Individual Normal Defined
- Establishes a dynamic normal pattern per worker, role, team, and jurisdiction over time
- Baseline updates continuously — distinguishing genuine change from manipulation attempts
- Multi-dimensional baseline: time, volume, pace, location, tool usage, and output quality
Anomalies are only detectable against a known baseline — this layer builds it.
3
Adversarial Detection Engine
Manipulation Intelligence
- Identifies active manipulation tactics — not just statistical outliers
- Detects system gaming, rule exploitation, and coordinated fraud across accounts
- Recognises evolving threat patterns that adapt to avoid standard detection methods
Built to detect adversarial intent — not just unintentional deviation.
4
Risk Intelligence Engine
Decision-Grade Risk Assessment
- Each anomaly is scored for severity, confidence level, and financial exposure
- Recurrence probability determines whether this is an isolated event or a systemic pattern
- Risk intelligence drives proportionate response — low risk flagged, high risk controlled
Risk scores that drive action — not just alert counts that create noise.
5
Control & Response Engine
Active Control — Not Passive Monitoring
- System takes immediate automated action — does not wait for human review to begin
- Response is proportionate to risk — flagging, restriction, escalation, or re-verification
- Every control action is logged with a justification, risk context, and immutable audit trail
This is a control system. The response happens — with or without a human initiating it.
6
Evidence Chain Layer
Forensic-Grade Anomaly Records
- Every detected anomaly generates a structured evidence object — not just an alert log
- Raw activity data, pattern analysis, and detection logic are all embedded in the record
- Chain of custody, integrity hash, and immutable timestamp ensure court-defensible evidence
Every anomaly is a case — not an entry in a log file.
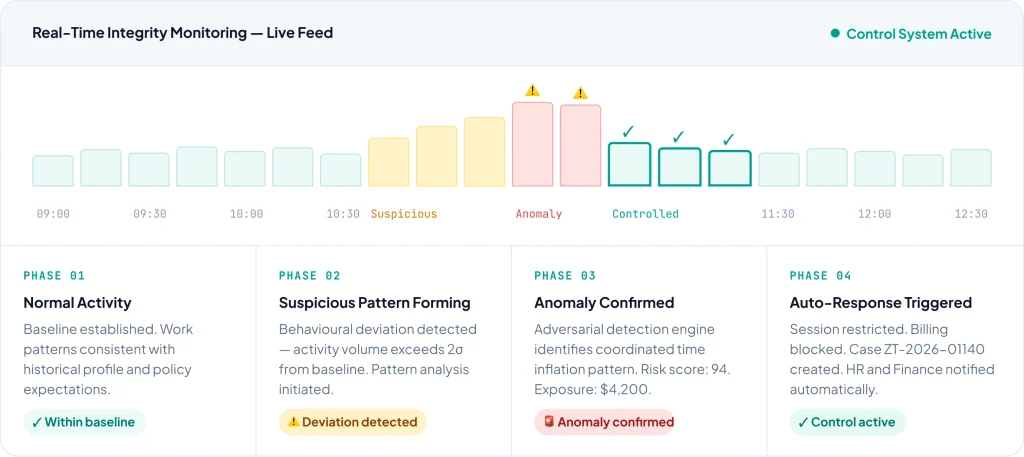
Detection Flow
From Activity to Controlled Response — In Seconds
The complete integrity lifecycle — from the moment a suspicious activity occurs to the point the control response is executed and the evidence record is sealed.
Integrity Control Lifecycle — Automated Flow
- 3 seconds end-to-end
01 — CAPTURE
Activity Captured
Every workforce event enters the verified input pipeline in real time — session, task, and context signals recorded.
02 — BASELINE
Compared to Baseline
Activity is measured against the individual's established behavioural baseline across all dimensions simultaneously.
03 — DETECT
Anomaly Detected
The Adversarial Detection Engine identifies a deviation. Manipulation tactic is classified. Pattern severity assessed.
04 — ASSESS
Risk Assessed
Risk score, confidence level, financial exposure, and recurrence probability are calculated — decision-grade intelligence.
05 — CONTROL
Control Triggered
Automated response is executed proportionate to risk level — flag, restrict, escalate, or require re- verification instantly.
06 — RECORD
Evidence Recorded
A tamper-evident evidence object is created — raw data, analysis, response, and chain of custody sealed and audit- ready.
Anomaly Coverage
Designed to Detect Real-World Manipulation
Each anomaly type has its own detection model, risk scoring framework, and financial impact calculation — built for the manipulation tactics that actually occur in enterprise workforces.

Behavioural Manipulation
Activity patterns gamed to appear productive — idle masking, artificial engagement signals, and pattern exploitation designed to avoid detection by standard monitoring tools.
Detection method
High Risk
Multi-dimensional behavioural baseline deviation analysis with adversarial pattern recognition

Temporal Exploitation
Time inflation tactics — clock manipulation, session extension without activity, and boundary exploitation at shift start and end — designed to inflate billable hours or payroll-eligible time.
Detection method
Critical
Temporal pattern analysis cross-referenced with output verification and session continuity signals

Location Inconsistency
Geographic anomalies — impossible travel between sessions, jurisdiction- mismatched location claims, and location spoofing that creates compliance gaps or triggers incorrect policy frameworks.
Detection method
High Risk
Cross-session location plausibility analysis with device and network signal correlation

Coordinated Activity
Multiple accounts or workers acting in coordination to manipulate platform metrics, inflate task counts, or game reward systems — invisible to per- account monitoring but detectable at network level.
Detection method
Critical
Network-level correlation of timing, device, output, and pattern signals across multiple accounts
Financial Impact Engine
Every Risk Translates to Financial Exposure
ZoikoTime does not just flag anomalies — it quantifies the financial exposure of each detected event in real time, giving CFOs and risk teams the intelligence they need to prioritise response and recover losses.

Estimated Loss Calculation
Real-time calculation of the financial value of each anomalous event — projected across the detection period at current billing or payroll rates.

Potential Exposure Modelling
If the anomaly is systemic — recurring pattern, coordinated group — total exposure is projected forward, surfacing the true scale of the risk before it compounds further.

Recovery Opportunity Identification
ZoikoTime identifies the period and transactions affected, enabling precise recovery actions — clawbacks, billing corrections, or payroll adjustments with full evidence backing.
Counterfactual Intelligence
What Would Have Happened Without ZoikoTime
Understanding the cost of inaction makes the value of control concrete — for every anomaly detected and controlled, there is a clear counterfactual of what the undetected version costs.
Without ZoikoTime
Manipulation Undetected
- Coordinated time inflation continues for 3+ months before appearing in a payroll reconciliation
- No audit trail exists — dispute resolution is based on conflicting claims, not verifiable evidence
- Business decisions made from manipulated data — resourcing, performance ratings, compliance reports
- Financial loss accumulates silently — each period compounds the total exposure
- Regulatory audit reveals data integrity failure — penalties applied, reputation damaged
Estimated undetected loss (90 days)
$63,900
Without ZoikoTime
Issue Detected Early — Controlled Immediately
- Anomaly detected on day 14 — 76 days of further loss prevented by immediate control action
- Complete forensic evidence record created automatically — dispute resolved in hours, not weeks
- Business data integrity maintained — decisions built on verified, manipulation-free records
- Financial exposure quantified immediately — recovery actions initiated with evidence backing
- Regulatory audit passed — complete integrity records provided on demand, no findings
Actual loss with ZoikoTime
$21,300
Human-in-Command
AI Detects. System Controls. Humans Decide.
ZoikoTime automates detection and control at machine speed — while ensuring human judgement governs every consequential outcome, investigation, and resolution.
STEP 01
Detection
AI-powered detection engines identify anomalies, classify manipulation tactics, and surface behavioural patterns in real time — across every worker and region simultaneously.
STEP 02
Risk Scoring
Every detected anomaly is assessed for severity, financial exposure, and recurrence probability — producing decision- grade risk intelligence that prioritises human attention on what matters most.
STEP 03
Control Action
Automated control is executed proportionate to risk — session restrictions, billing blocks, and escalation triggers fire immediately without requiring human initiation, preventing further loss.
STEP 04
Human Review
The right human — HR, compliance, finance, or legal — receives a fully evidenced case with risk context, financial exposure, and control history, enabling informed decisions without starting from zero.
Enterprise Impact
Direct Impact on Risk and Revenue
Measurable outcomes for the executives accountable for financial integrity, systemic risk, and audit defensibility.
CFO
Prevent Financial Leakage
Real-time anomaly detection and automated billing controls prevent payroll inflation, fraudulent task claims, and time manipulation from impacting financial records — with quantified exposure visibility at all times.
CRO
Reduce Systemic Risk
Adversarial detection — coordinated fraud, pattern exploitation, and evolving manipulation tactics — reduces systemic integrity risk across the entire workforce, not just individual incidents.
Internal Audit
Gain Forensic Visibility
Every anomaly generates a forensic evidence record — structured, integrity-verified, and audit-ready — providing complete visibility into detected incidents with no manual reconstruction required.
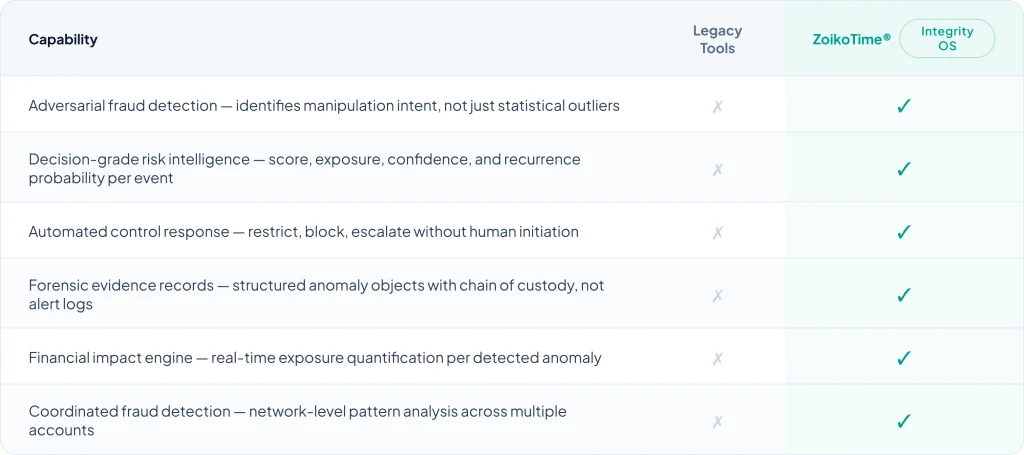
Why ZoikoTime
Why Monitoring Tools Fail to Protect Integrity
Monitoring tools observe. ZoikoTime controls. Observation without response is not protection — it is documentation of failure.
Get Started
If You Cannot Control Integrity, You Cannot Control Risk
ZoikoTime gives your organisation the adversarial detection intelligence, automated control infrastructure, and forensic evidence capability needed to protect the integrity of every workforce decision — before manipulation reaches your financial records.
