Security Overview
Security Engineered for
Enterprise Assurance, Control and Trust
ZoikoTime is designed with a security-first architecture that protects workforce data, enforces policy-driven access, and maintains system integrity across distributed environments.
Security is not a feature. It is a continuously validated system of controls, monitoring, and accountability.
Security Positioning
Security as a Core System Layer
ZoikoTime embeds security across identity, data, infrastructure, and operations. Controls are enforced through policy, validated continuously, and supported by audit-ready evidence — not implemented as a feature set bolted onto a workforce product.
Security controls are enforced, validated, and monitored — not assumed.
This means every security control has three properties: it is actively enforced at the system level; it is continuously tested to confirm it is functioning as designed; and it is monitored in real time to detect any deviation from expected performance. These are verifiable claims — not policy commitments.
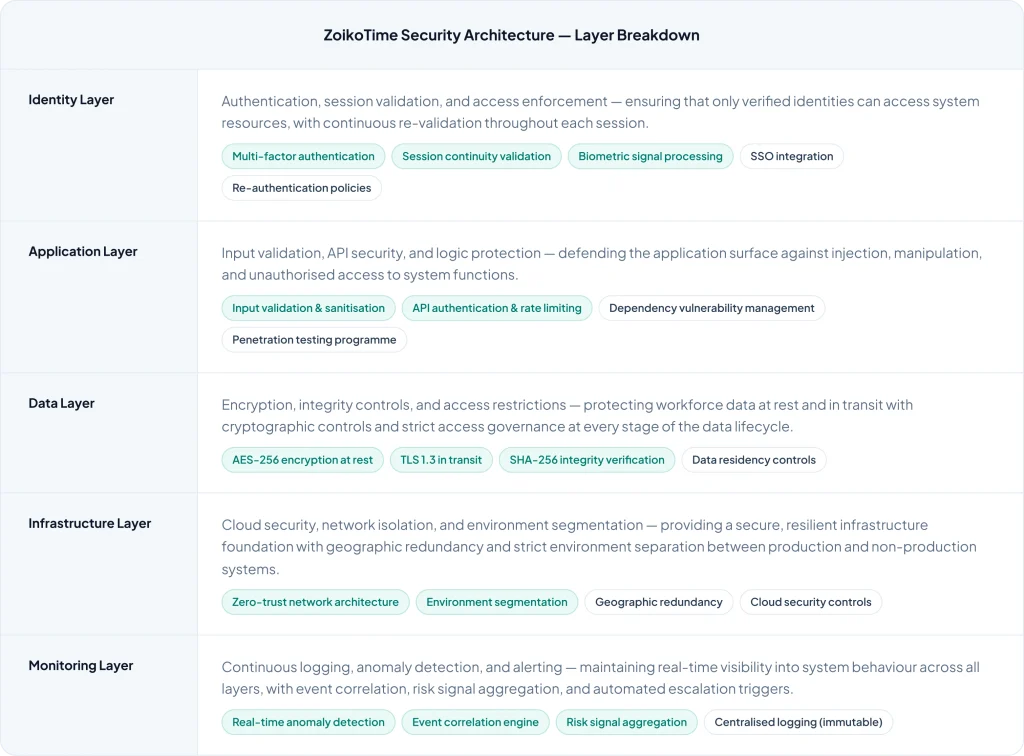
Security Architecture
Layered Security Architecture
Five security layers — each defending a distinct system boundary, each with defined controls, risk mitigations, and enforcement mechanisms.
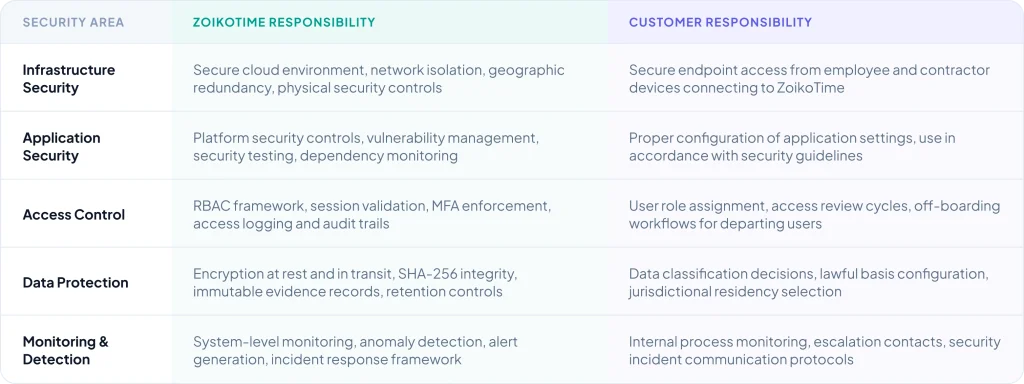
Shared Responsibility
Shared Responsibility Model
Enterprise security requires clarity about who is responsible for what. The ZoikoTime shared responsibility model defines the boundary between platform and customer obligations — essential for enterprise due diligence.
Identity & Access
Identity and Access Management
A comprehensive IAM model — least privilege enforcement, session-level validation, and enterprise identity provider integration built in from the start.

Role-Based Access Control
Every user, role, and system component operates with the minimum access required for their function. Cross-scope data access is prevented at the architecture level — not dependent on user behaviour.

Multi-Factor Authentication
MFA is enforced for all user access — configurable per role and risk profile. Session timeout and re-authentication policies are applied based on inactivity and elevated risk signals detected during active sessions.

Enterprise SSO Integration
Native integration with enterprise identity providers — Okta, Azure AD, Google Workspace, and other SAML 2.0 / OIDC compatible systems. Single sign-on with centralised identity governance from your existing IdP.

Access Logging
Every access event is logged — immutably and with full context. Role, timestamp, resource accessed, session state, and outcome are recorded for every interaction, providing a complete access audit trail for any review period.

Session Controls
Configurable session timeout and automatic re-authentication policies — applied based on role, risk profile, and inactivity detection. Session continuity monitoring detects anomalous access patterns in real time.

Privileged Access Management
Elevated privileges are managed through time-limited grants, approval workflows, and enhanced monitoring — no standing privileged access that could be exploited through credential compromise or insider risk.
Data Protection
Data Protection and Lifecycle
Data is protected at every stage — from ingestion to retention. A five-stage lifecycle model with security controls enforced at each boundary.
Ingestion
Data enters via secure, validated channels — TLS 1.3 enforced, input validation applied, source authentication required before any data is accepted into the processing environment.
Processing
Validated and processed within controlled, isolated environments — access restricted to processing functions with least- privilege enforcement. No data commingles across tenant boundaries.
Storage
AES-256 encrypted at rest with strict access controls. Data residency configurable per jurisdiction. SHA-256 integrity verification applied to all evidence records at storage and on retrieval.
Access
Restricted via RBAC and policy — every access event is logged immutably. Purpose limitation enforced at system level: data cannot be accessed beyond the stated governance function.
Retention
Jurisdiction-aware retention policies applied automatically — data retained for exactly as long as required by law and no longer. Deletion certificates provided at end of lifecycle.
Data is protected at every stage — from ingestion to retention — with security controls enforced at each lifecycle boundary, not applied selectively.
Threat Model
Threat Model and Risk Approach
Five threat categories, each with specific mitigations built into the system architecture — demonstrating security thinking maturity to CISOs, security reviewers, and procurement teams.
Unauthorised Access
- Mitigated by RBAC, MFA, session controls
Least-privilege access, mandatory MFA, session validation, and continuous access monitoring prevent both external attackers and insider threats from gaining access beyond their authorised scope.
Data Exposure
- Mitigated by encryption and access restriction
AES-256 at rest, TLS 1.3 in transit, and strict access controls at every data boundary ensure that workforce data cannot be exposed through network interception, storage breach, or unauthorised access.
Insider Risk
- Mitigated by audit logs and access controls
Immutable audit logs, least-privilege enforcement, and role-scoped access controls limit the blast radius of insider risk and provide the forensic evidence required to detect, investigate, and resolve incidents.
System Abuse
- Mitigated by anomaly detection
Continuous anomaly detection identifies system abuse patterns — unusual access volumes, off-hours activity, configuration changes, and API misuse — before they can be exploited to extract data or disrupt operations.
Infrastructure Attack
- Mitigated by cloud security and isolation
Zero-trust network architecture, environment segmentation, and cloud- native security controls defend the infrastructure layer — with geographic redundancy ensuring availability even under distributed attack scenarios.
Supply Chain Risk
- Mitigated by vendor evaluation and monitoring
Third-party vendor risk management includes security evaluation before onboarding, restricted access scoping, dependency vulnerability monitoring, and ongoing oversight — reducing supply chain attack surface.
Incident Response
Incident Response Framework
A structured, five-phase incident response framework — with defined escalation pathways, communication protocols, and evidence preservation requirements at each stage.
PHASE 01
Detection
Anomaly detection and monitoring systems identify incident signals — automated alert generation with risk classification and initial scope assessment.
PHASE 02
Containment
Immediate isolation of affected systems or users — preserving evidence integrity while limiting further exposure. Escalation to security team initiated.
PHASE 03
Investigation
Root cause analysis using audit logs, anomaly data, and access records — full forensic investigation with chain of custody maintained throughout.
PHASE 04
Resolution
Remediation of root cause, restoration of affected systems, verification that controls are functioning correctly — with evidence documentation of actions taken.
PHASE 05
Post-Incident Review
Structured review of detection effectiveness, response time, and control performance — with recommendations incorporated into the continuous improvement programme.
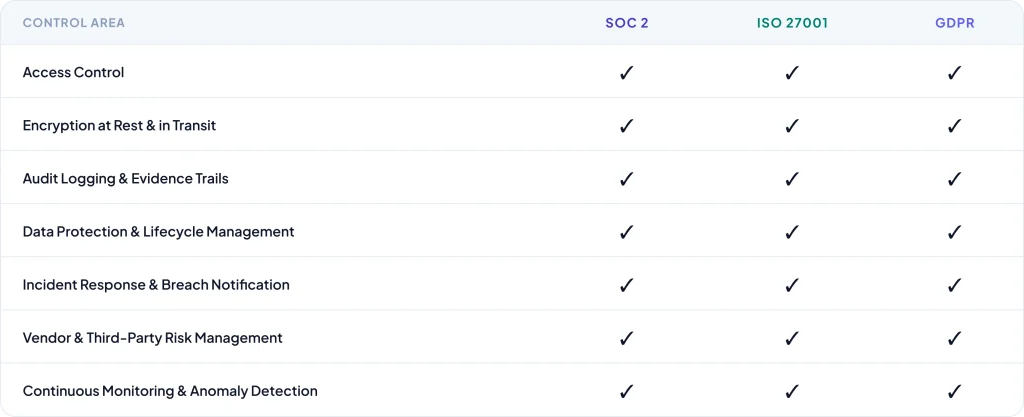
Control Alignment
Control Alignment with Security Standards
Every ZoikoTime security control is mapped to SOC 2, ISO 27001, and GDPR requirements — providing the audit-friendly evidence that compliance teams and security reviewers need.
Security Resources
Security Documentation & Downloads
Everything your security, legal, and procurement teams need — structured for due diligence, available immediately.

Security Overview
Complete security architecture overview, controls documentation, and assurance statement — structured for CISO and security review.

Architecture Brief
Technical architecture documentation, data flow diagrams, and security boundary definitions for CTO and infrastructure review teams.

Compliance Summary
SOC 2, ISO 27001, and GDPR control alignment summary — structured for procurement and legal due diligence review teams.

Shared Responsibility Model
Complete shared responsibility definition — ZoikoTime vs. customer obligations for every security domain, for procurement clarity.
Security Contact
Security Contact & Responsible Disclosure
For security enquiries, enterprise security reviews, or responsible disclosure of vulnerabilities.

Enterprise Security Enquiries
For enterprise customers, security reviewers, and procurement teams requiring detailed security documentation, architecture walkthroughs, or customised security assessments.

Responsible Disclosure
ZoikoTime operates a responsible disclosure programme — if you have identified a potential security vulnerability, please report it through our secure disclosure channel. We commit to acknowledging all reports within 24 hours and providing regular updates throughout the investigation.
Enterprise Confidence
Security Designed for Enterprise Confidence
ZoikoTime provides the continuously validated security architecture, controls documentation, and audit-ready evidence that enterprise security teams, procurement reviewers, and regulators require.
