Privacy Controls
Privacy Built Into System Design Governed, Controlled, and Transparent
ZoikoTime enables organisations to manage workforce data responsibly through policy-driven controls, transparent practices, and alignment with global privacy standards.
ZoikoTime is not a surveillance system. It operates within employer-defined policies and is designed to support lawful, transparent, and accountable workforce management.
Privacy Positioning
Privacy as a System-Level Requirement
ZoikoTime embeds privacy into system design, ensuring that data collection, processing, and access are governed by policy, constrained by purpose, and supported by user rights — from the first line of code to the final evidence record.
Privacy controls are not a feature set that can be toggled off. They are architectural requirements that cannot be bypassed by configuration, individual discretion, or operator policy.
Privacy is enforced through system design, not dependent on individual discretion.
This means every privacy control has three properties: it is enforced at architecture level; it cannot be bypassed by user or admin action; and it is continuously validated to confirm it is functioning as designed. These are verifiable system properties — not policy statements.
Lawful Basis
Lawful Basis for Data Processing
GDPR and equivalent privacy frameworks require a lawful basis for every data processing activity. ZoikoTime's default processing activities and their applicable lawful bases are documented below.
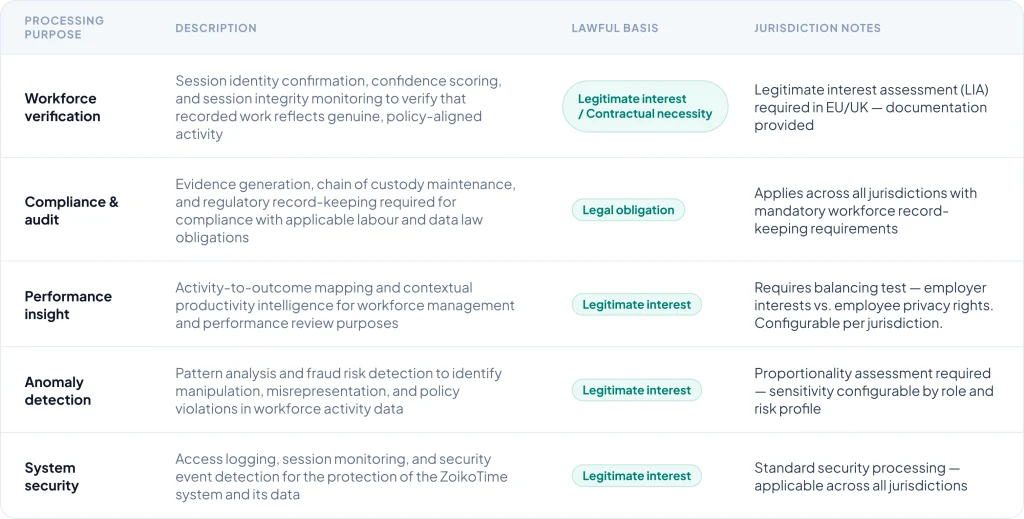
Important note: The applicable lawful basis depends on jurisdiction, the employer's specific policies, and applicable regulatory requirements. ZoikoTime provides the framework and documentation — the deploying organisation is responsible for confirming the appropriate lawful basis in their specific legal context with qualified legal counsel.
Roles & Responsibilities
Roles and Responsibilities in Data Use
ZoikoTime operates under a three-party model — clearly defining the distinct responsibilities of the employer, the ZoikoTime platform, and the employee or user.

Employer
- Defines the policies and governance model that ZoikoTime enforces
- Configures system behaviour, thresholds, and sensitivity levels
- Determines the applicable lawful basis for processing in their jurisdiction
- Responsible for notifying workers of ZoikoTime deployment and usage

ZoikoTime Platform
- Enforces the policies defined by the employer — no independent determination of data use
- Applies privacy controls at system level — data minimisation, purpose limitation, access restrictions
- Maintains system integrity and generates audit-ready evidence records
- Provides the technical infrastructure for user rights exercise and transparency

Employee / User
- Interacts with ZoikoTime through session recording and the Transparency Center
- Retains all applicable privacy rights under their jurisdiction's law
- Can view what signals are collected and how their confidence score is calculated
- Can exercise data subject rights through defined channels at any time
ZoikoTime does not independently determine how workforce data is used. It enforces policies defined by the organisation — within the bounds of applicable privacy law and ZoikoTime's own privacy architecture requirements.
Data Lifecycle
Data Lifecycle and Control Points
Every stage of the data lifecycle has a defined control, governing policy, and risk mitigation — applied automatically, not selectively.
Collection
Only minimum required signals. No surplus data collection by design.
Processing
Processed only for stated purpose in isolated, controlled environments.
Retention
Automated retention per law. Deletion certificates provided at end of lifecycle.
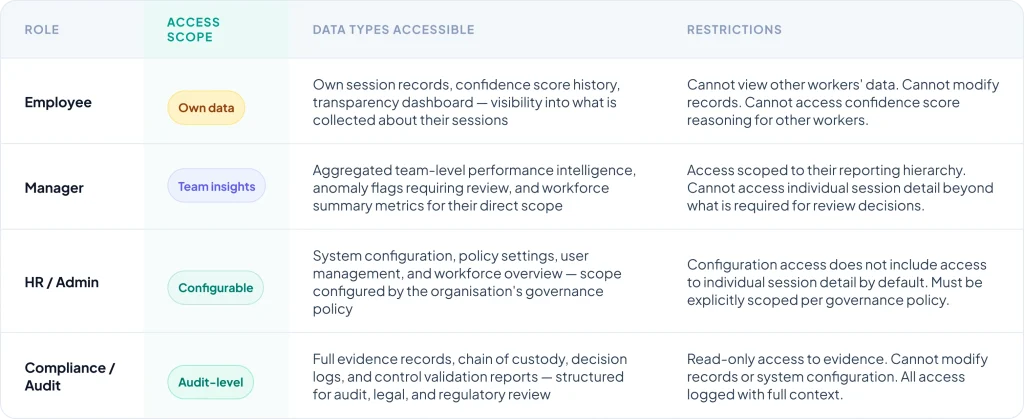
Access Model
Who Can Access What
Role-based visibility scoping ensures that data access is proportionate to governance function — no role can access data beyond the scope required for their responsibilities.
Data Subject Rights
Exercising Privacy Rights
ZoikoTime supports all applicable data subject rights under GDPR and equivalent frameworks — through structured, documented, and traceable processes.

Right of Access
Individuals can request a copy of all personal data processed about them — structured in a human-readable format with full context about how each data point was used.
- Submitted via privacy portal or email request — processed within 30 days

Right to Correction
Inaccurate personal data can be corrected through a documented request process — with correction evidence maintained as part of the compliance record.
- Requests assessed against policy and processed within 30 days

Right to Deletion
Data deletion can be requested where legally applicable — subject to retention obligations for compliance and legal proceedings. Deletion certificates issued on completion.
- Assessed against retention obligations — processed within 30 days

Right to Restriction
Processing can be restricted in defined circumstances — such as during a dispute about accuracy or pending an objection. Restriction status maintained in the compliance record.
- Assessed on a case-by-case basis — processing paused pending resolution

Right to Object
Individuals can object to processing based on legitimate interest in defined circumstances — objections assessed against the balancing test and employer policy with documented outcomes.
- Objections assessed within 30 days with documented outcome

Right to Portability
Where applicable, personal data can be provided in a machine-readable format — enabling transfer to another controller in relevant circumstances under GDPR Article 20.
- Provided in JSON format — assessed for applicability per request
All data subject rights requests are initiated through defined channels, processed in accordance with policy, logged and tracked for audit purposes, and resolved within regulatory timelines. ZoikoTime provides the infrastructure — the deploying organisation is responsible for managing the rights request process for their workforce.
Compliance
Privacy Framework Alignment
ZoikoTime's privacy architecture is aligned to GDPR, UK GDPR, CCPA, and equivalent global privacy frameworks — providing the documentation evidence that compliance and legal teams require.
Transparency System
Transparency and Visibility
Privacy without transparency is not sufficient. ZoikoTime provides multiple layers of visibility — for workers, administrators, and governance teams — ensuring that data practices are never opaque.

Transparency Center
Every worker has access to a personal Transparency Center — showing what signals are collected in their sessions, how the confidence score is calculated, and what decisions have been made about their data. Accessible at any time, without requiring a formal request.

Audit Logs
Immutable logs of all data access events, processing decisions, and system actions — providing complete traceability for administrators, compliance teams, and data subject rights responses. All access logged with full context and timestamp.

Data Use Clarity
Clear documentation of what data is collected, why it is collected, how long it is retained, and who can access it — structured for both technical review and plain-language communication to affected individuals.
Privacy Resources
Privacy Documentation & Downloads

Privacy Overview
Complete privacy architecture documentation — controls, principles, and framework alignment — for legal and compliance review.

Data Processing Summary
Structured summary of all processing activities, lawful bases, and retention schedules — formatted for GDPR Article 30 compliance records.

Compliance Documentation
GDPR, UK GDPR, and CCPA alignment evidence — structured for legal due diligence, procurement review, and regulatory audit support.
Privacy Contact
Contact the Privacy Team

Data Protection & Privacy Enquiries
For questions about ZoikoTime's privacy architecture, data processing practices, DPIA support, or general privacy compliance enquiries from organisations evaluating or deploying ZoikoTime.

Data Subject Rights Requests
For individual workers exercising data subject rights — access requests, deletion requests, objections, and corrections are processed through the structured rights request channel with documented outcomes.
Privacy First
Privacy Designed for Trust, Control, and Compliance
ZoikoTime provides the privacy-by-design architecture, compliance documentation, and user rights infrastructure needed to manage workforce data responsibly — across every jurisdiction, every workforce type, and every governance requirement.
