Privacy Framework Built for
Transparency, Compliance, and Enterprise Trust
ZoikoTime provides a structured, privacy-first framework aligned with GDPR, CCPA/CPRA, and global data protection standards designed for regulatory clarity and enterprise deployment.
We process data only as instructed, only for defined purposes, and only within a governed and auditable framework.
- GDPR Article-Level Alignment
- Privacy-by-Design Architecture
- Data Subject Rights Enabled
- Audit-Ready Documentation
- No Hidden Processing
How Privacy Works in ZoikoTime
Every data point in ZoikoTime flows through a governed, auditable
process — from collection through to deletion. Nothing is processed outside this structured framework.

Data Input
Minimum required signals only

Lawful Basis
Controller-defined, documented

Policy Definition
Organisation- configured rules

Processing
Purpose-limited, isolated

Controls & Logging
Immutable audit trail

Output
Role-scoped, explainable

Retention/Deletion
Jurisdiction-aware schedule
Every data point processed in ZoikoTime is governed by lawful basis, policy controls, and immutable audit logging — from first input to final deletion.
Clear Allocation of Responsibility
GDPR and equivalent frameworks require clarity about who makes decisions about data and who processes it on instruction.
ZoikoTime operates exclusively as a data processor — never as an independent data controller.
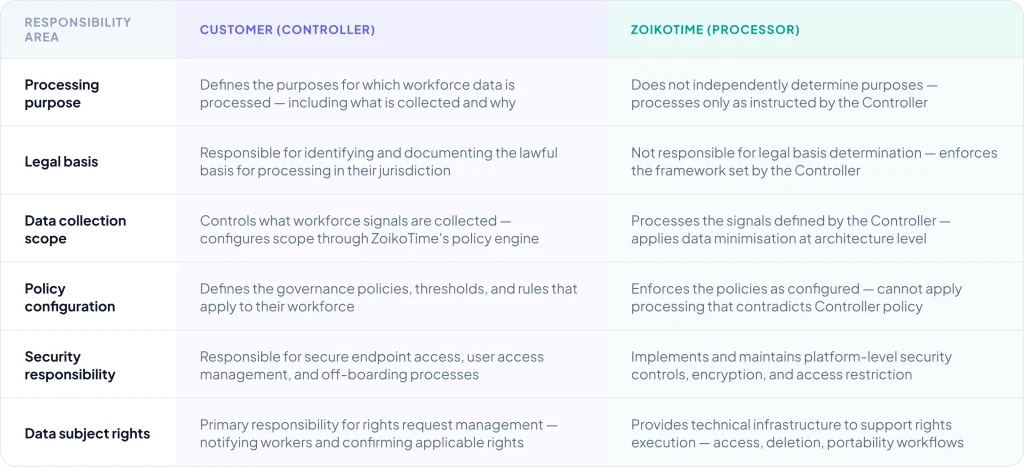
ZoikoTime does not independently determine purposes of processing. Every processing activity is governed by Controller instruction within the ZoikoTime policy framework.
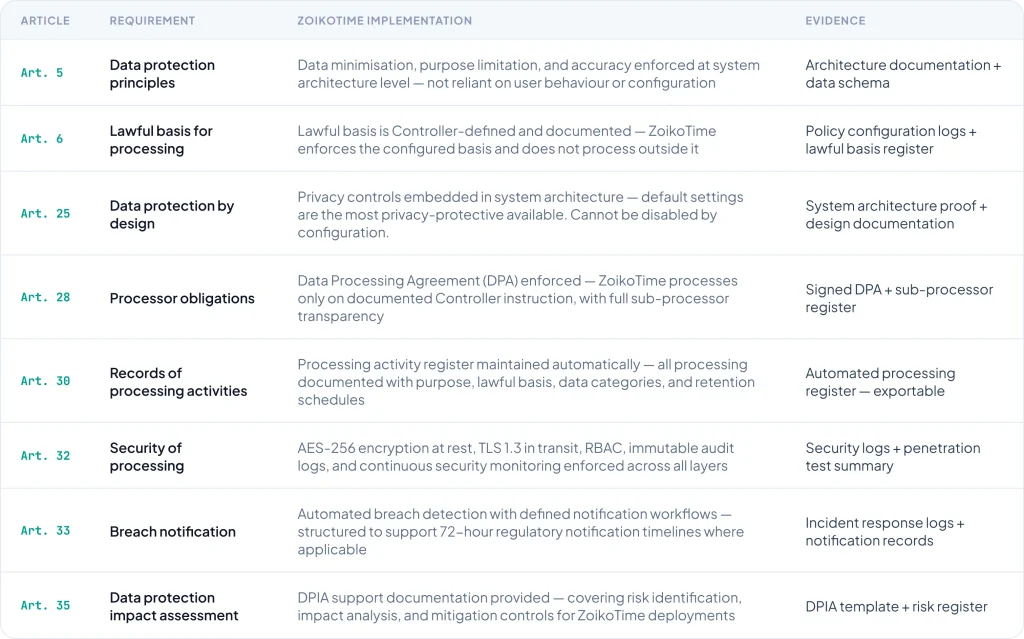
Article-Level GDPR Mapping
Regulator-grade clarity — every applicable GDPR article mapped to its
corresponding ZoikoTime implementation, with the evidence generated to support each requirement.
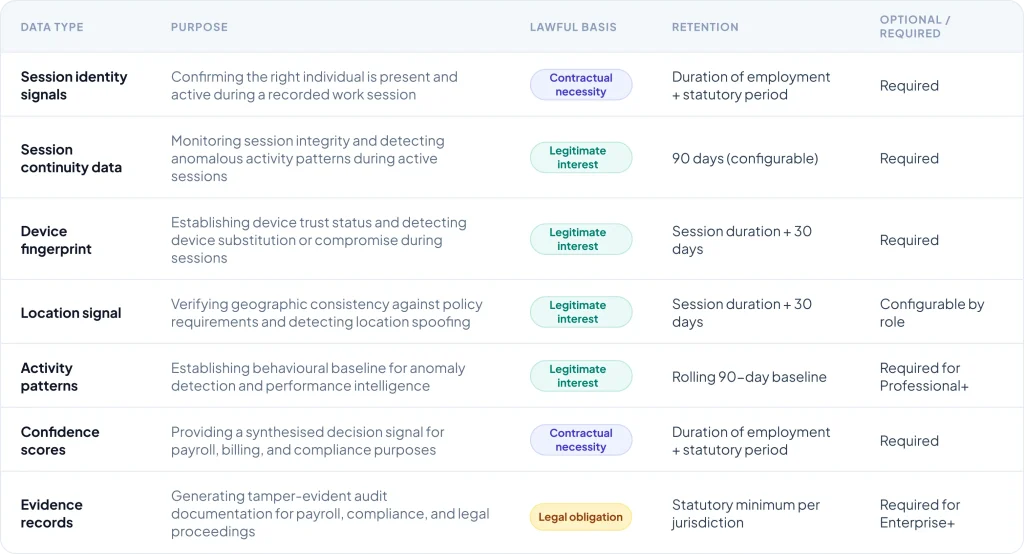
Data Categories and Purpose Mapping
Every category of data processed by ZoikoTime is documented with its
purpose, lawful basis, and retention schedule — structured to support DPIA requirements and regulatory review.
Data Sharing and Disclosure
ZoikoTime does not sell workforce data. Sharing is limited to defined
sub-processors, legally required disclosures, and Controller authorised integrations.

Sub-Processors
ZoikoTime uses a limited set of vetted sub-processors — exclusively for infrastructure, security, and operational functions. A complete, up-to-date sub- processor list is maintained and available to enterprise clients on request. Sub-processors are contractually bound to equivalent privacy standards.

Legal Disclosures
ZoikoTime may disclose data where required by applicable law, court order, or regulatory authority — with disclosure limited to the minimum information legally required. Where permissible, Controllers are notified of disclosure requests before fulfilment.

No Unauthorised Sale
ZoikoTime does not sell, license, or otherwise commercially exploit workforce data — under any circumstances. Data is processed exclusively for the purposes instructed by the Controller, within the framework defined in the Data Processing Agreement.
Cross-Border Data Handling
Where workforce data is transferred across jurisdictional boundaries,
ZoikoTime implements appropriate safeguards aligned to applicable transfer mechanisms.

Standard Contractual Clauses
EU Standard Contractual Clauses (SCCs) — 2021 module — are implemented for transfers from the EEA to third countries. UK International Data Transfer Agreements (IDTAs) are used for UK-origin transfers where applicable.

Jurisdiction-Aware Storage
Data residency is configurable per deployment — allowing enterprise clients to specify where workforce data is stored and processed. Residency controls are enforced at infrastructure level, not reliant on configuration correctness.

Transfer Impact Assessments
ZoikoTime maintains Transfer Impact Assessments (TIAs) for all material third- country transfer scenarios — available to enterprise clients for their own data protection compliance documentation.
Your Rights Under Applicable Law
ZoikoTime supports the full scope of data subject rights under GDPR,
UK GDPR, CCPA/CPRA, and equivalent frameworks — executed through structured, documented, and auditable processes.

Access (Art. 15)
Receive a copy of all personal data processed about you — structured and human-readable, with full context about each data category, purpose, and retention schedule.

Rectification (Art. 16)
Request correction of inaccurate personal data — with a documented correction record maintained as part of the compliance audit trail.

Erasure (Art. 17)
Request deletion of personal data where legally applicable — subject to retention obligations for legal proceedings and compliance. Deletion certificates issued on completion.

Portability (Art. 20)
Receive personal data in a structured, machine-readable format — enabling transfer to another controller where applicable under GDPR Article 20.

Restriction (Art. 18)
Restrict processing in defined circumstances — such as pending accuracy verification or objection assessment. Restriction status recorded in the compliance audit log.

Objection (Art. 21)
Object to processing based on legitimate interest — objections are assessed against the applicable balancing test with documented outcome and escalation if required.
How Data Subject Rights Requests Are Handled
A structured, five-stage workflow — ensuring every request is verified,
processed, responded to, and logged within regulatory timelines.
01

Request Received
Via privacy portal, email, or designated channel
02

Identity Verified
Proportionate verification before any data release
03

Request Processed
Data retrieved, suppressed, deleted, or corrected
04

Response Issued
Within 30 days (extendable by 60 days for complexity)
05

Audit Log Created
Request, outcome, and timeline recorded immutably
All requests are logged and processed in accordance with applicable law. ZoikoTime supports Controller execution of data subject rights — the Controller is the primary responsible party for rights management in their organisation.
Technical and Organisational Security Measures
Article 32 GDPR requires appropriate technical and organisational
measures. ZoikoTime implements a layered security model mapped to ISO 27001, SOC 2, and GDPR requirements.

Encryption
AES-256 at rest and TLS 1.3 in transit — applied to all workforce data from capture through to deletion. SHA-256 integrity verification on evidence records.

Access Control
Role-based access control (RBAC) with least-privilege enforcement — no cross- scope access. All access events logged immutably with full context.

Continuous Monitoring
Real-time anomaly detection, event correlation, and centralised logging across all system layers — with automated alerting on security signal deviation.

Audit Logging
Immutable audit logs for all data access, processing decisions, and system actions — structured for SOC 2, ISO 27001, and GDPR Art. 32 compliance review.
Operate With Confidence in Data Privacy
ZoikoTime provides the privacy framework, compliance documentation,
and audit-ready evidence needed to deploy workforce assurance infrastructure with complete regulatory confidence.
